Update from 26.03.2020 – 14:00
Did the hacker "palesa" possibly unmask himself? In a file, the name Manish Prashanth can be found in the code under the pseudonym "palesa". If you look curiously at LinkedIn, you will find a trained programmer of the same name: https://www.linkedin.com/in/manish-prashanth-19980523/. Coincidence or stupidity?
 Thanks to Peter for pointing 🙂
Thanks to Peter for pointing 🙂
Original News
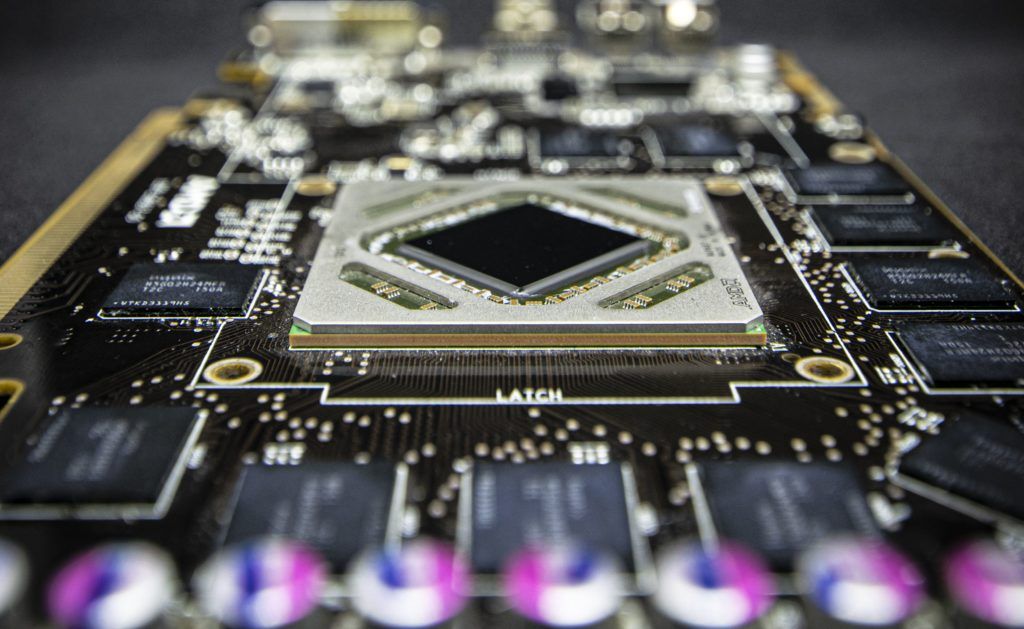
Yesterday, AMD reported a massive theft of its GPU IP in the form of source code posted by a hacker after the theft at Github and also posted on other websites, including TorrentFreak and 4Chan. The hacker, who is named Palesa, told TorrentFreak that the information is worth at least 100 million dollars because the source code contains information about AMD's current and future GPUs such as Navi 21, 10 and Adren (Xbox Series X).
AMD has since also announced that the current and next-generation GPU IPs have been stolen. Although the information has not yet been released, the source code for AMD is very critical because it contains not only the information for the current generation of GPUs, such as the RDNA 1-based Navi 10 GPU, but also for the next-generation GPUs, the RDNA 2 Navi 21 and the Adren SOC for Microsoft's Xbox Series X.
The dissemination of this stolen data would ultimately not only negatively affect the competitiveness of AMD's GPU products, but would also affect the security aspects of a product that will be used in more than one million devices in the coming years. would be accommodated. The question remains as to what would be more serious.
At AMD, data security and the protection of our intellectual property are a priority. In December 2019, we were contacted by someone who claimed to have test files related to a subset of our current and future graphics products, some of which were recently posted online, but have since been taken down.
While we are aware the perpetrator has additional files that have not been made public, we believe the stolen graphics IP is not core to the competitiveness or security of our graphics products. We are not aware of the perpetrator possessing any other AMD IP.
We are working closely with law enforcement officials and other experts as a part of an ongoing criminal investigation. Source: AMD
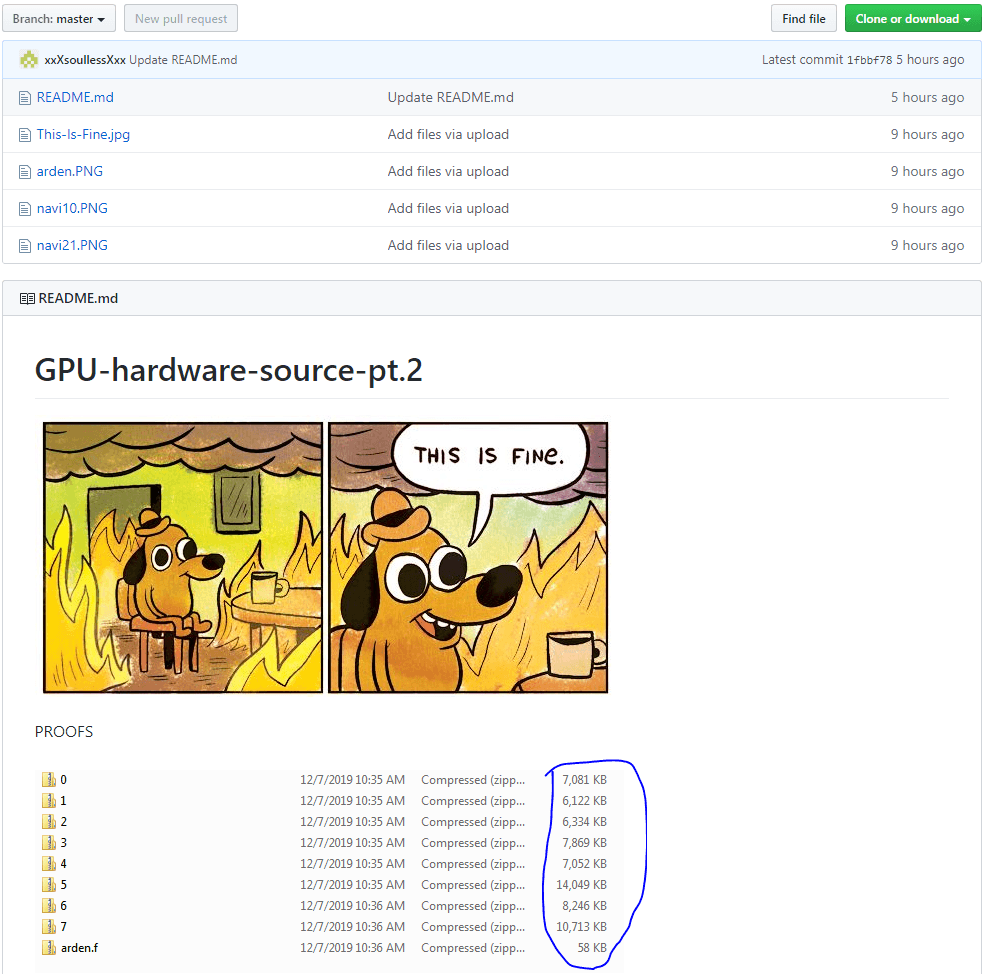
The hacker has since released the 2nd Update posted on Github after his first post was removed. This image screen copy of Github served as evidence:
It is interesting that the hacker wants to have this information downloaded from a completely unprotected server. TorrentFreak also reported that the hacker contacted her for the first time and reported that the information was worth at least 100 million dollars. In the latest update, however, the hacker has stated that he is not claiming this 100 million dollars, but would be willing to negotiate with AMD for a financial expense compensation via mail
"If I get no buyer I will just leak everything," the leaker concluded, adding that the files would be secured with passwords that will only be handed out to select individuals."
But in case no one wants to pay for it or AMD doesn't turn to the hacker in time, the hacker has announced that the information will be released to everyone free of charge. Previously, the hacker explained that the files were initially backed up with passwords that were only distributed to selected people, but they would be removed and all content shared.
While the original Github repository where the information first appeared was removed fairly firmly from the open source website because AMD had made a DCMA request, it was re-uploaded shortly thereafter. According to the hackers, the information dates back to November 2019, and there may well be a possibility that these are not the only three GPU source codes downloaded from AMD's servers.
It remains to be seen what will develop in the end.
Source: Github, Torrentfreak, wccftech


























Kommentieren